Nobody planned to steal $3 million from Sri Lanka.
They planned to steal $500,000. Once. Quietly. And then disappear.
But it worked so well the first time that they came back. And then came back again. And by the time anyone noticed, three separate government departments had sent money to three different fraudulent accounts. The total? Somewhere north of $3.1 million. Across three countries. Over more than two years.
And not a single firewall was breached.
No server was hacked. No password cracked. No sophisticated malware deployed. Just emails. Carefully written. Patiently timed. And a payment process that trusted email more than it should have.
This is the story of what happened in Sri Lanka between 2024 and 2026. It is also the story of what is happening right now in company finance departments, government treasury offices, and payment teams all over the world. Including India.
Act-1: The First Email Arrives
It starts, as these things always do, with someone doing their job.
Sometime in late 2025, an official at Sri Lanka’s External Resources Department received an email. It appeared to come from the Australian creditor agency. Sri Lanka had recently restructured its foreign debt after a severe economic crisis, and repayment schedules to various countries were active and ongoing. The email was about one of those scheduled payments.
The message said the bank account details had changed. New account number. New SWIFT code. Please update before the next instalment.
This is the moment. Right here. This is where the entire attack either succeeds or fails.
The official had doubts. Credit them for that. They reached out to verify. But they verified by replying to the same email thread. And that email thread was controlled by the attacker.
The attacker confirmed their own fake account details.
The payment was processed.
| The Sri Lankan government did everything right by their own procedures. They verified. They confirmed. They followed protocol. The protocol just had a fatal gap: it trusted email to verify email. |
Five instalments went out between December 2025 and March 2026. Each one landed in a fraudulent account in Delaware, USA. Total: $2.5 million.
The Australian creditor waited. The payments never arrived. Weeks passed.
Then Australia called.
Act-2: The phone call that revealed everything
In January 2026, Australian export finance agencies informed Sri Lankan officials that the payments had not been received.
There was, one imagines, a very long silence on that call.
Sri Lanka had sent the money. Sri Lanka had the confirmation emails. Sri Lanka had followed the process. And yet Australia had nothing.
Investigators were called in immediately. Sri Lanka’s Computer Emergency Readiness Team. The Criminal Investigation Department. The Financial Intelligence Unit of the Central Bank. Reports were filed. Agencies engaged.
And then, while reviewing recent transactions to figure out what had happened, someone noticed something.
There had been another attempt. A very similar request to change account details, this time for a payment due to India. Someone had looked at it more carefully. The account change looked suspicious. The India payment was paused.
The pause triggered a deeper look at all recent transactions.
That is when they found Australia. And that is when the real scale of what had happened started to become clear.
| What the investigation found:
The attackers had used look-alike email domains, addresses that appeared almost identical to the genuine creditor but with subtle differences. In one documented variant, the letter “i” in “australia” had been replaced with the number “1”. austral1a instead of australia. One character. Invisible at a glance. Enough to route all replies to the attacker. |
Four senior officials at the Public Debt Management Office were suspended. Criminal investigations began. The FBI was contacted. Australian Federal Police joined the probe. Interpol was engaged to trace the funds through international banking channels.
Part of the money was traced to that Delaware bank account. Recovery, investigators warned, would be complex. BEC attackers move money fast, through layered accounts designed to make it untraceable.
Act-3: The second fraud nobody knew about
Four days after the Treasury story broke publicly, Sri Lanka’s Cabinet Spokesman stepped to the podium for a regular media briefing.
Sri Lanka’s Department of Posts had been sending payments to the United States Postal Service for years as part of international postal operations. Standard. Routine. Completely unremarkable.
Except that somewhere along the way, the email address they were using for USPS payment instructions had been compromised. Not the official one registered with the Universal Postal Union. A different one. A fraudulent one that someone had quietly inserted into the communication chain.
The payments had been going to the wrong account for two years.
The breakdown, as investigators later revealed, was staggering in its patience. Roughly $900 in 2024, just enough to test that the account was working. Then $400,000 in February 2025, when the attackers grew confident. Then another $190,000 in October 2025. Total: approximately $625,000. Gone. To the USA. To an account the USPS had never seen.
| The attacker had been testing the system for a year before they went for the real money. They started with $900. When nobody noticed, they took $400,000. This is not an opportunistic crime. This is patient, professional, calculated fraud. |
The USPS, like the Australian creditor before them, had eventually noticed the payment had not arrived. They had informed Sri Lanka. An investigation had begun quietly. And then the Treasury story broke, and suddenly there were two separate missing payments to explain.
And a third attempt on India that had been stopped just in time.
| The FBI’s view on BEC:
The FBI has consistently identified Business Email Compromise as one of the most financially damaging types of cybercrime globally. In recent years, BEC attacks have generated billions of dollars in losses annually, surpassing ransomware as the top source of cybercriminal profit. The attacks work because they do not rely on technical sophistication. They rely on trust, process gaps, and the natural human tendency to believe that a professional email from a known sender is legitimate. |
What actually went wrong, and why it matters for you
Before we get to what everyone can do differently, it is worth being honest about what created the conditions for this attack. Because none of these conditions is unique to Sri Lanka.
The Treasury was in the middle of a transition. Responsibility for debt management was moving from the Central Bank to a newly created department. New staff. New processes. Experienced people had moved on. The incoming team did not yet know what normal looked like. Attackers specifically look for transition periods. They are windows of reduced institutional knowledge and relaxed scrutiny.
Email was the only channel. The entire payment authorisation process ran on email. No phone verification. No secure portal. No physical documentation. When something looked suspicious, the verification method was to send another email. To the attacker.
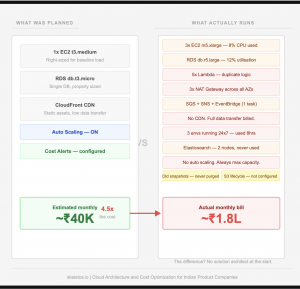
Legacy systems with no modern controls. Technology experts in Sri Lanka were publicly critical of the systems in use for sovereign debt management. No multi-factor authentication. No email authentication protocols. No automated flags for changes in payee account details.
The postal fraud ran for two years because nobody was cross-checking. The payments went out. The USPS presumably sent acknowledgements, or did not. Nobody reconciled the actual receipts against the payments made. Two years of fraud, sitting in plain sight in the accounts, undetected until the Americans complained.
What every person needs to know right now
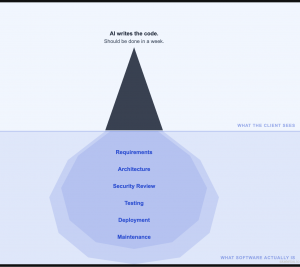
This is not a story about government incompetence in a small island nation. This is a playbook that is being run against finance teams, procurement departments, accounts payable teams, and individuals everywhere.
Here is what you personally need to understand and practise.
- The phone call rule. Any email requesting a change to bank account details, payment routing, or beneficiary information must be verified by phone. Not by replying to the email. Not by using a phone number provided in the email. By calling a number you already have, from a previous communication, from a business card, or from a known contact. If you cannot reach the person at a known number, do not process the change until you can. Full stop.
- Check the email domain carefully. Before you reply to any email involving money or sensitive information, look at the actual email address, not just the display name. The display name can say anything. “James Thornton, Export Finance Division” can be set by anyone. The actual address, the part after the @ symbol, tells you the truth. Learn to see it. ‘austral1a’ is not Australia. ‘g00gle’ is not Google. One character. That is all it takes.
- Urgency is the mechanism. Every BEC attack uses urgency. The payment must go today. The deadline is tomorrow. The account change is effective immediately. This urgency is manufactured. Its only purpose is to stop you from pausing to think. Whenever an email about money creates a sense of urgency, slow down. The legitimate counterparty can wait two hours while you verify through a separate channel. If they cannot, that itself is a red flag.
Personal level: WhatsApp voice cloning and fake family emergencies. BEC is not only a corporate problem. The same technique is being used against individuals. You receive a WhatsApp message from your son saying he has lost his phone and needs money urgently. The voice note sounds exactly like him. It is not him. It is a cloned voice generated from audio scraped from his social media. Before you send money to anyone claiming to be a family member in distress, call their actual number. If they do not answer, call someone who would know if they were in trouble.
What every business must implement
For organisations that handle any financial transactions, these are not suggestions. They are the minimum standard required to not become the next case study.
- Two-person authorisation for any payment change. No single person should have the authority to process a change to payee bank details alone. Two people, from different parts of the organisation, must independently verify and approve. If one person is manipulated, the second is a checkpoint. This is the single highest-impact change most organisations can make.
- Out-of-band verification for high-value transfers. For any payment above a defined threshold, require a confirmation through a second channel before funds are released. A call to a registered number. A confirmation through a secure portal. A physical sign-off. Email alone is not sufficient for transfers above a threshold your organisation defines.
- Implement email authentication protocols. SPF, DKIM, and DMARC are three technical standards that, when properly configured, make it dramatically harder for attackers to send emails impersonating your domain or trusted partners. Your IT team can implement these. They are not expensive. Most organisations, including many government departments, have not fully deployed all three.
- Reconcile payments against receipts regularly. The postal fraud ran for two years because nobody cross-checked whether the USPS had actually received the money Sri Lanka sent. Every organisation that makes recurring international payments should have a process to confirm receipt, not just confirm sending. Monthly reconciliation with counterparties is not bureaucracy. It is basic financial hygiene.
- Train your people on BEC specifically. General cybersecurity awareness training is not enough. Your finance team, procurement team, accounts payable staff, and anyone who processes payments need specific training on Business Email Compromise. What it looks like. What are the red flags? What to do when something feels slightly off. Most people who fall for BEC attacks are not careless. They are experienced professionals operating in high-volume, time-pressured environments. Training gives them the framework to pause at the right moment.
- Be especially vigilant during transitions. New staff, new systems, reorganisations, leadership changes. These are the moments attackers choose deliberately. Build extra verification steps into any period when institutional knowledge is being transferred. Make it policy, not an instruction that gets forgotten in the chaos of change.
The number that puts this in perspective
Sri Lanka lost at minimum $3.1 million across these three incidents. That is the confirmed number. The actual number may be higher as investigations continue.
The FBI reports that BEC attacks cost organisations globally billions of dollars every single year. More than ransomware. More than data breaches. More than any other single category of cybercrime.
And the reason BEC generates more money than all of those other attacks combined is not sophistication. It is simplicity. An email is free to send. A look-alike domain costs a few dollars to register. And a finance officer who is processing fifty payments a week, under deadline pressure, may look at a request to update bank details and see routine administration rather than the setup for a theft.
The entire defence against this class of attack is not a technology purchase. It is a habit change. A culture change. Two minutes of verification on the phone before a large payment is processed.
That call is inconvenient. The Sri Lanka story shows exactly what skipping it costs.
At Skeletos IT Service LLP, we work with Indian businesses on cybersecurity awareness, email security, and protection against exactly these kinds of attacks. If your organisation processes payments based on email instructions and has not reviewed its verification procedures, reach out. A conversation costs nothing. The alternative might.