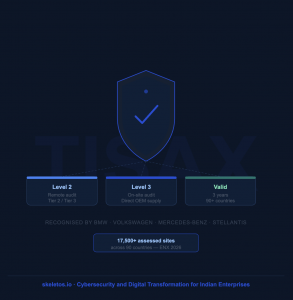
At Skeletos, innovation and optimization are at the heart of our DevOps practices. While speed and agility are crucial for success, security remains paramount. Today, we want to address the growing concern of security vulnerabilities within DevOps pipelines, and share the best practices we implement to ensure a secure flow from code to production.
The Evolving Threat Landscape:
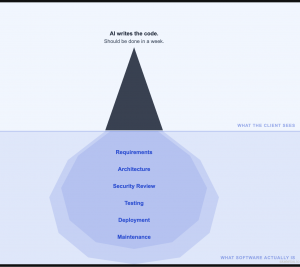
DevOps pipelines, by nature, automate many tasks, potentially creating new attack vectors. Unsecured code repositories, misconfigured infrastructure, and lax access controls can become easy entry points for malicious actors. The consequences can be devastating, leading to data breaches, application downtime, and reputational damage.
Building a Secure Pipeline:
Here are some key best practices we follow at Skeletos to mitigate these risks:
- Secure Coding:
- Shift Left Security: Integrate security practices early in the development lifecycle. Train developers on secure coding principles, like input validation and secure libraries.
- Static Code Analysis: Utilize static code analysis tools to identify and address potential vulnerabilities before code enters the pipeline.
- Dynamic Application Security Testing (DAST): Regularly scan applications for vulnerabilities during development and testing phases.
- Vulnerability Management:
- Continuous Vulnerability Scanning: Integrate vulnerability scanning tools into your pipeline to identify and prioritize vulnerabilities in infrastructure and applications.
- Patch Management: Implement automated patching processes to swiftly address identified vulnerabilities.
- Container Security: Secure container images by minimizing privileges, using verified registries, and scanning for vulnerabilities before deployment.
- Access Control:
- Principle of Least Privilege: Grant users only the minimum access required to perform their tasks.
- Identity and Access Management (IAM): Implement robust IAM solutions to control access to resources and infrastructure.
- Multi-Factor Authentication (MFA): Enforce MFA for all user accounts to add an extra layer of security.
- Continuous Monitoring and Logging:
- Monitor Pipeline Activity: Continuously monitor pipeline activity for suspicious behavior and potential security breaches.
- Log Centralization and Analysis: Centralize and analyze logs from all pipeline stages to identify anomalies and security incidents.
- Incident Response: Establish a clear incident response plan to quickly address and contain security breaches.
Beyond the Tools:
Remember, security is not just about tools and technologies. It requires a cultural shift within your organization. Promote security awareness among all employees, foster a culture of shared responsibility, and regularly review and update your security practices.
Conclusion:
By implementing these best practices, we can build secure and efficient DevOps pipelines. At Skeletos, we believe secure software is not just an option, it’s a necessity. By prioritizing security throughout the development process, we can deliver trusted solutions to our clients and build a foundation for sustainable growth.
Ready to Build a Secure DevOps Pipeline?
Connect with Skeletos today for a free DevOps consultation! Our team of security experts will assess your current security posture and recommend tailored solutions to mitigate risks and build a secure and efficient DevOps pipeline.
Schedule your consultation now and experience the Skeletos difference!