A few months ago, I was speaking with the owner of an auto component manufacturer based in PCMC. Good company. ISO 9001 certified. Strong quality systems. They had been chasing a German Tier 1 supplier for almost a year.
They finally got a serious response. The German company was interested. Asked for a few documents.
One item on that list: TISAX assessment results.
By the time they figured out what it was and how long it takes to get certified, the German client had moved to another supplier. One that already had the certificate.
I have heard this story, or some version of it, at least four or five times in the last year. Always from good manufacturers. Always a painful moment. And almost always avoidable.
So what exactly is TISAX?
If you work in manufacturing and have European clients or are trying to get them, you need to know this.
TISAX stands for Trusted Information Security Assessment Exchange. It was created by the German automotive industry association, the VDA, in 2017. The reason was simple: every major European car maker had its own security questionnaire for suppliers. BMW wanted one thing. Mercedes wanted another. Volkswagen had its own format. If you were supplying three OEMs, you were doing three separate security assessments every year. Expensive, repetitive, and exhausting.
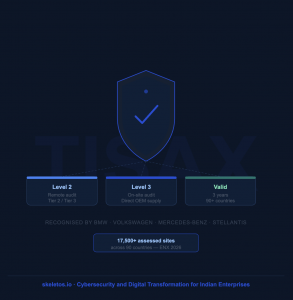
TISAX fixed that. One standardised assessment. Results stored on a secure platform. Shared with whoever needs to see them. Valid for three years. Every major OEM in Europe recognises it.
Today, TISAX has over 17,500 assessed sites across 90 countries. It is not a niche European thing anymore. It is the language of trust in global automotive supply chains.
| The straightforward version:
TISAX is basically your factory’s proof that the sensitive information your European client shares with you, design files, prototype specs, and production data, will not leak. It says: our systems are secure, our people are trained, our processes are controlled. We take your data as seriously as you do. |
Why does a parts manufacturer need to worry about data security?
This is what plant managers ask me. “We make metal parts. Why do we need a data security certificate?”
Fair question. Here is the answer.
When a European OEM sends you a project, they send you a lot more than a purchase order. They send CAD or design drawings of components that have not been launched yet. They send tolerance specifications that represent years of engineering work. They send production process requirements. In some cases, they send software specifications for components that go into connected vehicles.
That information is extremely valuable. To them. And to their competitors.
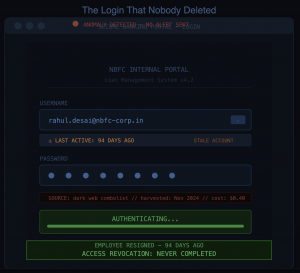
There have been real incidents where design data was stolen from supplier networks in India. Not because Indian companies are careless. Because their IT environments were not set up to protect data at the level European OEMs expect. And when that kind of incident happens, it does not just damage the supplier. It damages the OEM. It potentially delays a vehicle launch. It exposes confidential IP.
TISAX is the framework that says: when you share your data with us, here is exactly what we do to protect it.
The business case is actually quite simple
I know “compliance” sounds like cost and bureaucracy. But think about it differently.
Most Indian auto component manufacturers competing for European business are competing on price and quality. Those are table stakes now. Most decent manufacturers have both. So what breaks the tie?
Increasingly, it is trust and risk reduction for the buyer.
A procurement manager at a German OEM has to justify their supplier choices internally. Choosing a supplier without TISAX creates a compliance risk that they then own. They have to explain why they gave sensitive design data to a company without verified security controls. That is uncomfortable for them.
Choosing a TISAX-certified supplier removes that problem. The supplier has been assessed by an independent third party. The results are on record. If anything goes wrong, the OEM can show they did due diligence.
So when two suppliers are close on price and quality, the one with TISAX wins. Not because the procurement manager loves compliance. Because it makes their job easier and their risk lower.
One Tier 2 supplier I know in the Pune region told me their TISAX certification was specifically mentioned in the award letter from a German Tier 1. It was a three-year agreement. The investment in TISAX paid back in the first order.
What the assessment actually looks at
TISAX has three assessment levels. The one you need depends on what kind of information you handle for your client.
Most Tier 2 and Tier 3 suppliers in India will start with Assessment Level 2. This covers confidential information. The audit happens remotely. An assessor reviews your documentation, checks your evidence, and does a video interview with your information security lead. It is thorough but manageable.
Assessment Level 3 is for companies working directly with OEMs on prototype development, pre-launch vehicles, or safety-critical systems. This requires a physical site visit. If your client is a European OEM directly, this is probably where you need to aim.
The areas the assessment covers are not exotic. Physical security of your premises and server areas. Who has access to what systems? How you manage devices on your network. How you handle information shared by customers. How you train your employees. What do you do when something goes wrong? These are the fundamentals of running a secure IT environment. The assessment verifies that you are actually doing them, not just claiming to.
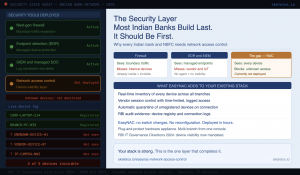
| The one area where Indian manufacturers consistently struggle:
Network visibility and access control. TISAX assessors want to see that only authorised users and devices can reach systems containing OEM data. In most factories I visit, sensitive CAD files and production data are accessible from the same network as personal phones, contractor laptops, and unregistered IoT devices on the factory floor. That is a serious gap for TISAX purposes, and it is one of the most common reasons Indian manufacturers fail or get significant findings in their first assessment. |
The mistakes I see IT managers make during preparation
I have sat with IT teams preparing for TISAX audits. The same mistakes keep showing up.
- The first is thinking that this is purely an IT job. It is not. TISAX requires action from HR, facilities, plant management, and senior leadership. IT cannot get physical access controls upgraded without facilities. IT cannot run information security training without HR. IT cannot set data handling policies without management approval. If the IT manager is the only person driving TISAX preparation, it will stall. This needs a senior project owner who can pull resources from across the organisation.
- The second is scoping everything at once. Companies try to bring every site, every system, every process into the TISAX scope in one go. Then it gets overwhelming, and nothing gets done. Start with one site, the one that directly handles OEM data. Get that certified. Then expand. A focused scope you can actually pass is worth more than an ambitious scope you cannot.
- The third is treating the audit as a destination rather than a checkpoint on a journey. TISAX assessors are not just checking if controls exist today. They are checking if they have been running consistently. Policies written the week before the audit, CCTV installed two weeks ago, and access logs going back only 30 days. None of that passes. You need at least three to four months of operational evidence. Compliance that exists only on paper is not compliance.
- The fourth is ignoring employee awareness. I have seen companies invest heavily in technical controls and completely forget that TISAX assessors will interview employees. Not just the IT manager. People in production, in admin, in procurement. They will be asked basic questions: what do you do if you receive an email with an attachment from an unknown sender? What is the process for reporting a security incident? If employees cannot answer these questions, it is a finding. Training your people is not optional.
- The fifth is leaving network segmentation too late. This is often the biggest technical gap in manufacturing environments. The production network with machines and sensors, the office network with computers and phones, and the server environment with confidential data are often on the same flat network. Anyone who gets onto any part of it can potentially reach everything. TISAX requires that systems containing OEM data be segregated and access-controlled. This takes time to design and implement properly. Starting this six weeks before the audit is not enough.
How long does it actually take?
Honestly, if you start from scratch with no existing ISMS, expect six to nine months to get to a point where you are ready for the assessment. If you already have ISO 27001 or have done serious work on your IT security posture, three to four months is realistic.
The cost varies. The ENX registration fee is fixed. The audit provider fee depends on the scope and assessment level. The internal cost of implementing controls is the biggest variable. Companies that try to cut costs by doing everything at the last minute usually end up spending more because they fail the first assessment, have to fix findings, and go through the process again.
Three to four months of honest preparation, done properly, with the right internal ownership, is the path that works.
Why Indian manufacturers should move on to this now, not later
European OEMs are actively looking to diversify their supply chains. The India opportunity in auto components is real and growing. But so is the competition from other markets.
The manufacturers who get TISAX now will have a genuine head start. Not just the certificate, but the relationships that come from being a trusted, verified supplier. European procurement managers remember which suppliers make their lives easy. They give more business to them over time.
The manufacturers who wait will find that their competitors have already built those relationships. And in supply chains, first-mover advantage compounds. It is much harder to displace a certified, trusted incumbent than to be the first certified supplier in the room.
The question is not whether TISAX will matter for your business. If you want European clients in the automotive sector, it already does. The question is whether you want to be ready the next time an inquiry lands, or whether you want to write another email saying you are working on it.
We have worked with manufacturers in the Pune, Chakan, and Nashik region on IT compliance and security readiness. If you want a practical, honest assessment of where your current setup stands against TISAX requirements, reach out. No obligation. Just a clear picture of the gap and what it takes to close it.
#TISAX #Manufacturing #AutoIndia #Compliance #CyberSecurity #EuropeanMarket #AutoComponent #MakeInIndia #SkeletosIT