Most IT managers and CISOs across Indian organisations don’t know exactly how many devices are connected to their network at any given moment. That gap — between what you think is on your network and what’s actually there — is where breaches begin…

The hidden attack surface in Indian organisations
The challenge is not that Indian companies are not investing in security. Most mid-sized and enterprise organisations have firewalls, antivirus, and increasingly, SIEM dashboards. The investment is there.
The problem is a visibility gap. You can have the best perimeter security in the world, but if you do not know what is actually connecting to your network from the inside, that perimeter means very little.
In the Indian context, this problem is amplified by a few specific factors. BYOD culture is deeply embedded here — employees routinely use personal phones for work WhatsApp groups, business email, and file sharing. IT teams are often stretched thin, managing security alongside a dozen other infrastructure responsibilities. And in manufacturing and industrial settings, operational technology (OT) devices like machine controllers and environmental sensors sit on the same network as business systems, often with no security controls at all.
The three entry points that most businesses are not guarding
1. BYOD — personal devices on corporate networks
Your employee’s personal Android phone connected to the office Wi-Fi has no corporate endpoint security, no patch management policy, and possibly carries malware picked up on a home or public network. In most Indian offices, this device gets the same network access as your finance systems or customer database. This is not a hypothetical risk — it is the current reality in the majority of organisations I visit.
2. IoT and operational technology devices
Smart cameras, HVAC controllers, access badge systems, and manufacturing floor sensors — these devices are typically installed by facilities or operations teams, without IT involvement. They run on outdated firmware, ship with default passwords that are never changed, and sit on the network for years without a single security patch. IoT breach attempts increased 84% in 2025. Attackers specifically target these devices precisely because they know nobody is watching them.
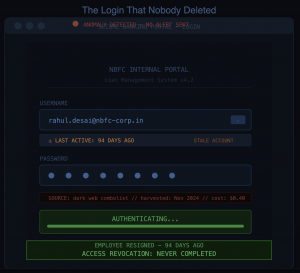
3. Former vendor and contractor access
A system integrator was given network access 14 months ago for an implementation project. The project ended. The access was never revoked. Dormant credentials sitting on your network are not a minor inconvenience — they are an open invitation. I have encountered this situation in nearly every mid-sized organisation I have visited across India.

What “Zero Trust” means for your business — without the jargon
“Zero Trust” has become one of the most overused phrases at every security conference in the last three years. But the underlying principle is genuinely important, and it does not require a technical background to understand.
Traditional network security assumes that anything inside your network is safe. Once a device is connected, it moves freely. Zero Trust rejects that assumption entirely. Every device must prove it meets your security standards before it is granted access. Every user must continuously verify their identity. The moment a device shows anomalous behaviour, its access is cut — automatically, in seconds.
Network Access Control — NAC — is the technology that makes Zero Trust operational rather than theoretical. It is the enforcement layer that continuously answers the question your security team should be asking every moment: who and what is on my network right now, and should they be here?
What NAC actually does — in practical terms
- Complete network visibility. NAC automatically discovers and profiles every device attempting to connect — managed or unmanaged, known or shadow IT. For the first time, you see your actual network, not just the one on paper.
- Policy-based access control. Before any device connects, NAC checks compliance — updated OS, active antivirus, encrypted storage. Devices that fail are automatically blocked or placed in a restricted zone. No manual intervention required.
- Role-based network segmentation. Contractors access only what their project requires — nothing adjacent. IoT devices are isolated in their own zone. Guest Wi-Fi is completely separated from internal systems. A compromised printer cannot reach your core banking application.
- Continuous monitoring and automated response. NAC does not just verify at the point of login — it continuously monitors every connected device. When anomalous behaviour is detected, the device is quarantined in seconds, before your team receives the first alert.
- Audit-ready compliance reporting. Every connection, every policy decision, every blocked device is logged and reportable. For RBI audits, CERT-In compliance reviews, or internal governance, the evidence is already prepared.
Why does this matter more in India’s regulated sectors
For most sectors, a breach is expensive. For Indian BFSI, NBFCs, payment gateways, and insurance companies, a breach is existential — combining regulatory action, customer trust collapse, and operational disruption simultaneously.
| Sector | Primary NAC risk | Regulatory exposure |
|---|---|---|
| Banks / BFSI | Unmanaged employee devices accessing core banking systems | RBI IT Governance Guidelines, CERT-In directions |
| NBFCs | Contractor access not revoked after project completion | RBI NBFC IT guidelines, data localisation rules |
| Payment gateways | IoT and POS devices on the same network as the payment infrastructure | PCI-DSS, RBI payment aggregator guidelines |
| Insurance | BYOD across distributed agent and branch networks | IRDAI cybersecurity guidelines 2023 |
| Manufacturing | OT/ICS devices with no authentication on production networks | CERT-In incident reporting, sector-specific MeitY guidelines |
The honest case for acting now
I understand the hesitation. Security budgets in India are finite, IT teams are stretched, and the ROI of a tool that prevents something that hasn’t happened yet is always difficult to justify to a CFO or board.
But consider the alternative framing: the question is not “can we afford NAC?” The question is “can we afford the consequences of not having it?”
An average breach in the Indian context — combining regulatory fines, incident response costs, reputational damage, and operational downtime — easily runs into crores. A single RBI or CERT-In compliance failure can trigger audits and directives that consume months of executive bandwidth. And the reputational damage to a bank, NBFC, or payment company following a publicised breach is extremely difficult to recover from in a market where customer trust is everything.
NAC is not an expensive enterprise-only tool. Modern solutions — particularly cloud-delivered ones — are deployable in weeks, not months, and are accessible to organisations of 50 people and above. The complexity and cost barriers that existed five years ago no longer apply.
If you are running IT security at a BFSI firm, NBFC, payment company, insurance provider, or manufacturing organisation in India — and you are not certain of every device currently on your network — that is worth addressing this month.
At Skeletos IT Services, we distribute and implement NAC solutions specifically for the Indian market. We start with a no-obligation network visibility assessment — no sales pitch, just clarity on where you actually stand.